Phishing in South Africa: How Attacks Work and How to Respond
Phishing has become one of the most widespread and damaging forms of cybercrime in South Africa. As a professional private investigation agency, PI INVESTIGATOR has seen a sharp increase in cases involving phishing scams targeting individuals, businesses, and even legal professionals.
With the rapid advancement of artificial intelligence, phishing has evolved into a far more sophisticated and dangerous threat. Distinguishing between legitimate communication and a malicious attempt to gain access or exploit you has become increasingly difficult, even for vigilant individuals.
South Africa is considered one of the most targeted countries globally for cybercrime, with millions of attacks detected annually and billions lost to fraud . What is particularly concerning is that most of these attacks are not technical hacks—but social engineering scams, where victims are manipulated into handing over sensitive information.
This guide explains how phishing attacks work in South Africa, how to identify them, and what to do if you fall victim—based on real investigative experience.
What is Phishing?
Phishing is a cybercrime technique where criminals impersonate trusted institutions—such as banks, government agencies, or well-known companies—to trick victims into:
- Revealing login credentials
- Providing banking details
- Clicking malicious links
- Downloading harmful attachments
The majority of BEC (Business Email Compromise) scams originate from sophisticated social engineering tactics. In many cases, criminals gain unauthorized access to your email account without your knowledge and remain undetected in the background. They monitor communications, waiting for the right opportunity to intercept an invoice, alter the banking details, and redirect payments that were intended for you.
These attacks typically occur via:
- Email (most common)
- SMS (smishing)
- WhatsApp messages
- Fake websites
- Social media platforms
At its core, phishing is a social engineering attack designed to exploit human trust rather than technical system vulnerabilities. Traditional antivirus software may not detect this type of unauthorised access, which is why two-factor authentication (2FA) is essential. Even if a scammer manages to obtain your password, the additional security layer significantly reduces the risk of access by requiring a second form of verification.
How Phishing Attacks Work in South Africa

1. Data Collection (Reconnaissance)
Criminals gather information about you from:
- Social media profiles
- Data breaches
- Public records
This allows them to craft highly personalised phishing messages.

2. The Bait (Impersonation)
You receive a message that appears legitimate, such as:
- “Your bank account has been suspended”
- “You have a parcel waiting”
- “Urgent SARS refund available”
These messages often mimic:
- Banking institutions
- Courier companies
Government departments
3. The Hook (Urgency & Fear)
Phishing messages create panic or urgency, forcing victims to act quickly:
- “Act within 24 hours or your account will be blocked”
- “Immediate verification required”
This psychological manipulation is the most effective tactic used by cybercriminals.

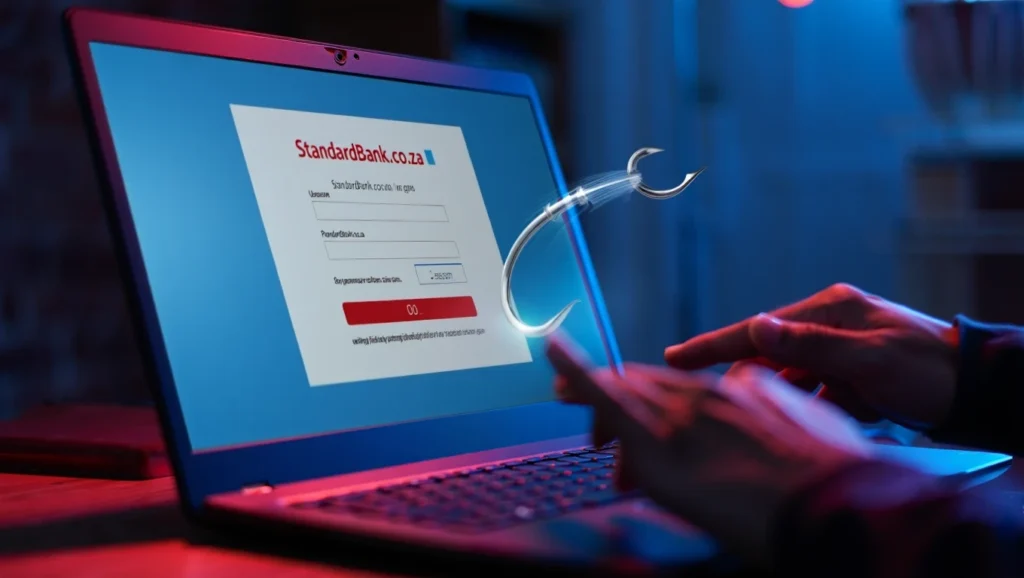
4. The Trap (Fake Website or Link)
Victims are directed to a fraudulent website that looks identical to the real one.
Once you enter your:
- Username
- Password
- OTP (One-Time PIN)
…the criminals gain full access to your accounts. Always inspect the URL carefully—this is often a clear indicator when verifying a site’s authenticity.

5. The Exploitation
Once access is gained, criminals:
- Transfer funds
- Take loans in your name
- Access business systems
- Conduct further scams using your identity
Divert payments, ect
Why Phishing is So Effective in South Africa
Phishing continues to grow due to several factors:
- High digital banking usage
- Increased mobile transactions
- Data leaks and poor password hygiene
- Human error and trust
- AI capabilities
According to SABRIC, over 65% of financial crime incidents involve digital fraud, most driven by social engineering tactics
Common Types of Phishing Scams in South Africa
1. Bank Phishing
Fake emails/SMS claiming:
- Account suspension
- Suspicious transactions
2. SARS Refund Scams
Victims are told they are owed a tax refund.
3. Courier/Delivery Scams
“Your package is on hold—click here to release it.”
4. Business Email Compromise (BEC)
Companies are tricked into:
- Paying fake invoices
- Changing supplier banking details
5. WhatsApp Phishing
Scammers impersonate:
- Friends or family
- Bank representatives
Red Flags: How to Identify a Phishing Attack
Be cautious if you notice:
- Urgent or threatening language
- Suspicious links (misspelled URLs)
- Requests for personal or banking details
- Poor grammar or unusual formatting
- Unexpected attachments
Golden Rule:
Banks and legitimate institutions will NEVER ask for your password or OTP.

What To Do If You Receive a Phishing Message
- Do NOT click any links
- Do NOT provide any information
- Verify directly with the institution
- Report the incident immediately
What To Do If You Have Fallen Victim
Step 1: Contact Your Bank Immediately
Your bank is your first line of defence. Request:
- Immediate freezing of transactions
- Reversal attempts
- Internal fraud investigation
Step 2: Report to Authorities
Report the incident to:
- South African Police Service
- South African Banking Risk Information Centre
Step 3: Preserve Evidence
Do NOT delete:
- Emails
- SMS messages
- Screenshots
- Transaction records
This is critical for investigation and legal proceedings.
Step 4: Change All Passwords
Immediately update:
- Banking credentials
- Email accounts
- Social media
Step 5: Engage a Professional Investigator
- Tracing digital footprints
- Identifying suspects
- Compiling court-ready evidence
- Supporting attorneys and legal teams
We operate across:
How PI INVESTIGATOR Assists in Phishing Cases
We take a structured, lawful, and evidence-driven approach:
- Digital forensic analysis
- IP and metadata tracing
- Financial transaction tracking
- Evidence preservation (chain-of-custody)
- Court-ready reporting
We are often called upon to testify in court proceedings, ensuring evidence stands up legally.
Prevention Tips: How to Avoid Phishing Scams
Essential Security Measures
- Enable 2FA (Two-Factor Authentication)
- Use strong, unique passwords
- Never click on unknown links
- Verify all financial requests
- Avoid public Wi-Fi for banking
Behavioural Awareness
- Slow down—phishing relies on urgency
- Question unexpected messages
- Confirm via official channels
Business Protection Tips
- Train staff on phishing awareness
- Implement email verification protocols
- Use secure payment verification processes
Frequently Asked Questions (FAQ)
1. What is phishing?
Phishing is a cybercrime where criminals impersonate trusted entities to steal personal or financial information.
2. Can phishing attacks be traced?
Yes. While criminals attempt to hide, they leave digital footprints that skilled investigators can trace.
3. Can a private investigator recover my money?
No investigator can guarantee recovery. However, we build strong cases, trace suspects, and assist legal recovery efforts.
4. How quickly should I act after being scammed?
Immediately. The first 24 hours are critical to limit financial loss.
5. Are phishing scams common in South Africa?
Yes. South Africa ranks among the most targeted countries for cybercrime globally.
6. Can phishing affect businesses?
Absolutely. Businesses are often targeted through invoice fraud and email compromise schemes.
7. Is it illegal to access someone’s messages to investigate phishing?
Yes. Under South African law (RICA), accessing communications without consent is illegal.
8. What evidence should I keep?
Keep:
- Emails
- Screenshots
- Bank records
- Communication logs
9. How do scammers make messages look real?
They clone legitimate websites and use branding identical to trusted institutions.
10. How can I protect myself long-term?
- Stay informed
- Use strong cybersecurity practices
- Seek professional advice when unsure
Final Word
Phishing is not just a technical threat—it is a psychological attack designed to exploit trust.
At PI INVESTIGATOR, we believe that education, prevention, and professional investigation are the strongest tools in combating cybercrime in South Africa.
If you suspect you’ve been targeted, act immediately—and consult professionals who understand both the technical and legal landscape.
adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
