The Reality of Online Scams in South Africa
Online scams are no longer isolated incidents—they are a daily reality affecting individuals, businesses, and professionals across South Africa. From phishing emails and fake investment schemes to WhatsApp impersonation scams, cybercriminals are becoming more sophisticated and more aggressive.
Recent data highlights the severity of the problem:
- South Africans lost approximately R3.3 billion to financial crime in 2023
- Digital banking fraud incidents increased by 86% in 2024
- As many as 57% of South Africans have been targeted by scams within a year
At PI INVESTIGATOR, we deal with victims of online scams daily. Whether in Johannesburg, Pretoria, Cape Town, or anywhere in South Africa, the impact is the same—financial loss, emotional distress, and uncertainty about what to do next.
Here is a complete guide on what to do when you were a victim of a online scam in South Africa.
Immediate Steps to Take After an Online Scam
1. Act Immediately – Time is Critical
The first few hours after discovering a scam are crucial. Many victims delay action due to shock or embarrassment—this is a mistake.
Immediate actions:
- Gather all the intelligence, bank account details, images, documents, etc before the suspect deletes all the critical information.
- Do not send additional money (even if threatened)
- Secure your accounts immediately
- Do not alert the suspect of your intention to report the crime
Cybercriminals often rely on panic and urgency to manipulate victims. Regain control quickly.

2. Contact Your Bank Immediately
If funds have been transferred, your bank is your first line of defence. Contact them immediately and request that the transaction be frozen. If the funds were transferred to an account at another bank, instruct your bank to urgently notify the receiving institution.
Advise your bank that you will be registering a criminal case and will provide the case number in due course. Ensure that you obtain a reference number for your report and request that the matter be escalated to an internal fraud investigator without delay.

3. Preserve All Evidence
Phishing messages create panic or urgency, forcing victims to act quickly:
Evidence is everything.
At PI INVESTIGATOR, we consistently see cases collapse because victims delete crucial information.
Do NOT delete:
• WhatsApp messages
• Emails
• Payment confirmations
• Screenshots
• Phone numbers
• Crypto wallet addresses
Properly preserved evidence strengthens:
• Criminal cases
• Insurance claims

4. Report the Crime to Authorities
You must open a criminal case.
Report to the South African Police Service (SAPS):
- Report a crime via SAPS
- Or visit your nearest police station
- Ensure your report is as detailed as possible, add all the documentary evidence, proof of payments, WhatsApp communications, etc
Here is the correct method to use when exporting WhatsApp messages which can be attached to your Police report (do not print screenshots).
Many cases fail due to poorly structured initial statements, making early professional guidance essential. Should you require assistance, contact PI INVESTIGATOR for a complimentary consultation—we will gladly guide you at no cost.

5. Secure Your Digital Identity
Scammers often steal more than money—they steal access.
Change immediately:
- Banking passwords
- Email passwords
- Social media accounts
- PINs and security questions
Enable:
- Two-factor authentication (2FA)
- Account alerts
Two-factor authentication (2FA) is a critical security measure that every individual should enable on their accounts. It is often overlooked, yet this simple step can be the key barrier between your profile and a scammer attempting to gain access. PI INVESTIGATOR strongly advocates that all users implement 2FA across all their accounts.

6. Notify Relevant Platforms
If the scam occurred on a platform:
- Facebook / Instagram
- Online marketplace
Report the account immediately.
This helps:
- Prevent further victims
- Preserve digital traces

7. Engage a Professional Cyber Crime Investigator
There is a common misconception regarding what a cyber crime investigator can and cannot do. Clients should be cautious of any party guaranteeing the recovery of funds. The primary role of a cyber investigator is to investigate the offence, identify the responsible parties, and compile evidence that is robust and admissible in court.
We also assist with the below:
- Trace digital footprints
- Analyse financial flows
- Identify suspects
- Compile court-ready reports
- Assist attorneys and law enforcement
Cybercriminals are not anonymous. They leave digital trails—IP data, device fingerprints, transaction patterns.
Understanding Online Scams in South Africa
Common Types of Scams
In South Africa, the most common scams include:
- Phishing (fake emails and login pages)
- Investment scams
- Romance scams
- Business email compromise (BEC)
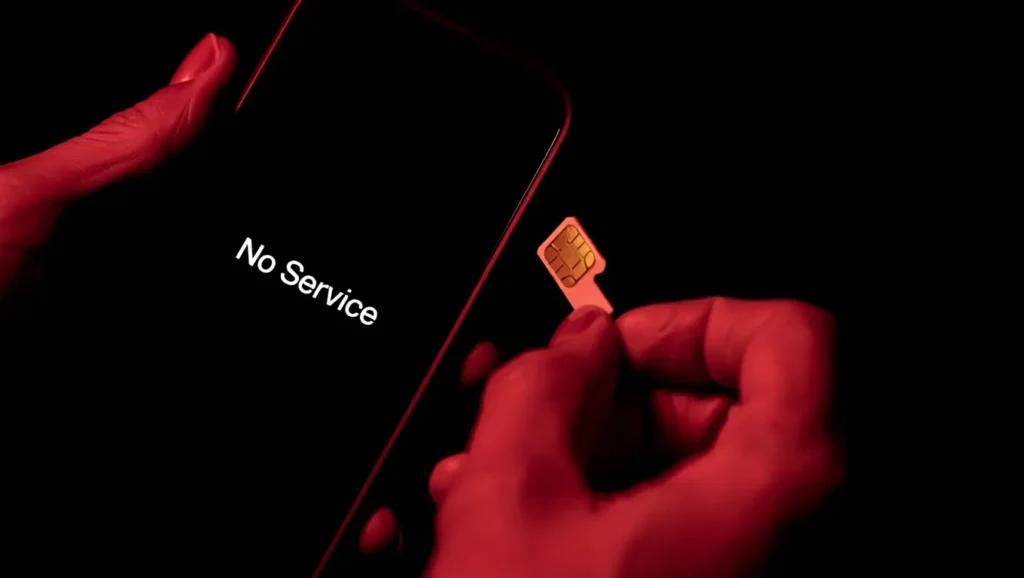
- SIM swap fraud
- Impersonation scams
Studies show phishing remains one of the most prevalent cybercrimes, affecting hundreds of thousands of victims annually
Why Online Scams Are So Effective
Modern scams are not random—they are strategic.
Criminals use:
- Social engineering
- Psychological manipulation
- Data leaks
- AI-generated profiles and deepfakes
Many attacks exploit human error, not technical weaknesses
How PI INVESTIGATOR Assists Victims
1. Digital Forensic Analysis
We analyse:
- IP logs
- Metadata
- Device signatures
2. Financial Tracing
We track:
- Bank transfers
- Crypto wallets
- Money mule accounts
3. Suspect Identification
Through:
- Data correlation
- Behavioural analysis
- Open-source intelligence (OSINT)
- Other methods we cannot divulge
4. Legal-Ready Reporting
- Structured
- Evidential
- Our reports are:
- Court-compliant
Prevention Tips: How to Avoid Online Scams
- Verify Before You Trust
Never trust:
- Urgent payment requests
- Unknown investment opportunities
- “Too good to be true” deals
- Be Wary of Pressure Tactics
Scammers create urgency:
- “Act now or lose everything”
- “Your account will be blocked”
Pause. Verify.
- Protect Your Personal Information
Never share:
- OTPs
- Banking details
- Passwords
- Monitor Your Accounts Regularly
Check:
- Bank statements
- Credit reports
Southern African Fraud Prevention Service (SAFPS)
- Use Strong Cybersecurity Practices
- Strong passwords
- 2FA enabled
Updated devices
Damage Control: If You Have Already Been Scammed
-
- Accept What Happened – Act Fast
There is no shame in being scammed. Criminals are highly sophisticated.
- Attempt Fund Recovery
Recovery depends on:
- Speed of reporting
- Transaction method
- Jurisdiction
- Prevent Secondary Victimisation
Many victims are targeted again by:
- Fake “recovery agents”
- Anyone who promises to recover your money is probably looking to scam you AGAIN!
Be cautious.
- Monitor Identity Theft Risks
Impersonation fraud has increased dramatically in South Africa. In 2024 it skyrocketed by 337%.
- Strengthen Your Digital Security
Treat this as a reset:
- New passwords
- New protocols
- Increased awareness
Our National Coverage
At PI INVESTIGATOR, we operate across South Africa:
- Johannesburg – Cyber Crime Investigator in Johannesburg
- Pretoria – Cyber Crime Investigator in Pretoria
- Cape Town – Cyber Crime Investigator in Cape Town
- Nationwide – Cyber Crime Investigator in South Africa
Frequently Asked Questions (FAQ)
1. What should I do immediately after being scammed?
Act quickly: contact your bank, preserve evidence, and report the crime.
2. Can stolen money be recovered?
In some cases, yes—especially if reported quickly. However, recovery is not guaranteed.
3. Can cyber criminals be traced?
Yes. Despite attempts to hide, digital footprints often lead to identification.
4. Should I report the scam to SAPS?
Absolutely. A criminal case is essential for any legal action.
5. Can a private investigator help with online scams?
Yes. A cyber investigator strengthens your case with professional evidence.
6. Is digital evidence admissible in court?
Yes—if collected legally and documented correctly by a registered private investigator or expert cyber crime investigator.
7. What if the scammer used cryptocurrency?
Crypto can be traced through blockchain analysis and exchange records.
8. How long does an investigation take?
It depends on complexity—some cases take days, others weeks or months.
9. Is your service confidential?
Yes. We operate under strict confidentiality and POPIA compliance.
10. How much does a cyber investigation cost?
Costs vary depending on complexity. Consultation is recommended to assess scope.
Final Word
Online scams are not just increasing—they are evolving. South Africa has become one of the most targeted regions for cybercrime in Africa .
The difference between loss and recovery often comes down to speed, expertise, and evidence.
At PI INVESTIGATOR, we specialise in uncovering the truth, protecting our clients, and delivering results that stand up in court.
If you have been a victim—act now.
