Business Email Compromise: First 24 Hours Playbook (South Africa)
Business Email Compromise (BEC) is one of the fastest-growing and most financially devastating cybercrimes affecting businesses in South Africa. From SMEs in Johannesburg to corporates in Cape Town and Pretoria, no organisation is immune.
These types of crimes are done when you least expect and could have a devastating effect on your business, especially small enterprises.Unlike traditional hacking, BEC is not about breaking systems — it is about manipulating trust.
Criminals infiltrate email systems silently. They observe. They wait. Then they strike — often intercepting invoices, changing banking details, and redirecting payments without raising suspicion.
By the time the fraud is detected, the funds have already been moved. Perpetrators deliberately create distance by using money mules, which makes tracing the primary offender significantly more challenging. In most cases, the individual identified is the account holder rather than the mastermind behind the scheme.
The first 24 hours are critical.
What you do — or fail to do — can determine whether funds are recovered, evidence is preserved, and perpetrators are identified.
At PI INVESTIGATOR, we specialise in cybercrime investigations across Johannesburg, Pretoria, Cape Town, and the whole of South Africa, assisting victims in building legally sound, court-ready cases.
What is Business Email Compromise (BEC)?
Business Email Compromise is a targeted cyber fraud where criminals gain unauthorised access to business email accounts or impersonate legitimate parties to manipulate financial transactions.
Common BEC Scenarios:
- Invoice interception and bank detail manipulation
- CEO fraud (urgent payment instructions from “executives”)
- Supplier impersonation scams
- Payroll diversion schemes
- Legal or property transaction fraud
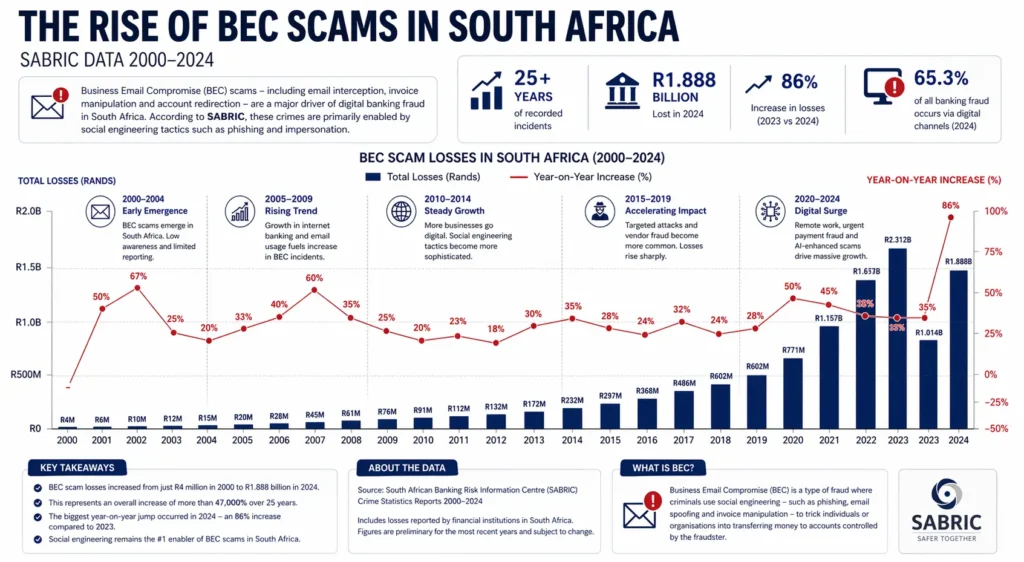
According to South African Banking Risk Information Centre, this type of crime has increased by approximately 86% year-on-year, with losses reaching around R1.888 billion. The majority of these incidents are driven by social engineering — the primary barrier scammers must overcome. These schemes require little to no technical hacking skill; they rely on deception, most commonly through phishing attacks.
How BEC Attacks Work (The Anatomy of the Scam)
Phase 1: Access
Criminals gain access through:
- Phishing emails
- Weak passwords
- Data breaches
Lack of two-factor authentication (2FA)

Phase 2: Silent Monitoring
They monitor:
- Email conversations
- Payment cycles
- Supplier relationships

Phase 3: Execution
At the right moment:
- They intercept an invoice
- Change banking details
- Send it from a compromised or spoofed email

Phase 4: Payment Diversion
Funds are transferred to:
- Mule accounts
The First 24 Hours Playbook (Critical Response Plan)
Hour 0 – 2: Immediate Damage Control
When you discover a BEC incident, act immediately:
✅ 1. Contact Your Bank (Urgent)
- Request an immediate freeze or recall
- Provide transaction details
- Ask them to alert the receiving bank
✅ 2. Notify the Receiving Bank
- Your bank must initiate this
- Speed is critical — delays reduce recovery chances
✅ 3. Secure Your Email Systems
- Request your webmail administrator to preserve all access logs and filters created in the backend.
- Change all passwords immediately
- Enable 2FA across all accounts
- Log out all active sessions
- Do not communicate on the compromised email
Hour 2 – 6: Evidence Preservation
- Preserve Digital Evidence
Do NOT delete anything.
Secure:
- Emails (including headers)
- Payment confirmations
- IP logs
- Server logs
✅ 5. Identify the Breach Point
- Which account was compromised?
Was it internal or supplier-side?

Hour 6 – 12: Legal & Criminal Action
- Consult a cyber crime expert
Once you have alerted your bank, you will typically be advised to open a case at your nearest police station. While this is the standard process, the reality is that many cases struggle to progress SAPS having limited resources, technical capacity, and the availability of actionable evidence.
In many instances, victims arrive at this stage without the necessary documentation or digital evidence to support a successful investigation. As a result, cases often stall or fail to gain traction.
At this point, it is important to proceed carefully rather than rushing ahead. A more strategic approach is to first consult a cybercrime investigator who can guide you on preserving evidence, structuring your case correctly, and ensuring that any information presented is admissible and useful. This early intervention can significantly improve the likelihood of a meaningful outcome.

Hour 12 – 24: Containment & Strategy
- Notify Affected Parties
- Suppliers
- Clients
- Internal teams
✅ 9. Conduct Internal Risk Assessment
- Identify other vulnerabilities
- Audit financial controls
✅ 10. Implement Immediate Safeguards
- Dual payment verification
- Banking detail confirmation protocols (This in itself is not sufficient)
Email security upgrades

Why Speed is Everything in BEC Cases
Funds move quickly through:
- Multiple bank accounts
- International transfers
- Cryptocurrency channels
Delays of even a few hours can make recovery extremely difficult.
According to the Association of Certified Fraud Examiners, organisations lose approximately 5% of annual revenue to fraud, with BEC being a major contributor.
Prevention: How to Avoid Business Email Compromise
1. Enable Two-Factor Authentication (2FA)
This is non-negotiable.
Even if passwords are compromised, access is blocked.
2. Verify Banking Detail Changes
Always:
- Call the supplier directly
- Use verified contact numbers
3. Train Staff on Social Engineering
BEC is a human vulnerability attack.
Awareness is your first line of defence.
4. Use Strong Email Security
- Spam filters
- Domain protection (DMARC, DKIM, SPF)
5. Monitor Email Activity
- Unusual logins
- Forwarding rules
- Login locations
How PI INVESTIGATOR Assists Victims
We are not recovery agents making false promises.
We are professional investigators focused on:
- Identifying perpetrators
- Tracing funds
- Building admissible evidence
Our Process:
- Digital forensic analysis
- Email header tracing
- Financial intelligence mapping
- Chain-of-custody documentation
- Legal report compilation
We are often called upon to testify in court proceedings, ensuring that the evidence we gather stands up to scrutiny.
Frequently Asked Questions (FAQ)
1. Can stolen funds be recovered after a BEC scam?
Recovery is possible, but it depends on how quickly action is taken. If funds are frozen early, there is a higher chance of recovery. Delays significantly reduce success rates.
2. Can a cybercrime investigator recover my money?
No legitimate investigator can guarantee recovery. Our role is to investigate, trace, and build a legal case — not make unrealistic promises.
3. How do criminals access business emails?
Through phishing, weak passwords, lack of 2FA, or prior data breaches.
4. Is BEC considered a criminal offence in South Africa?
Yes. It falls under fraud and is governed by legislation such as the Cybercrimes Act.
5. Can digital evidence be used in court?
Yes, if collected lawfully and properly documented with chain-of-custody.
6. What is the most important step in the first 24 hours?
Contact your bank immediately to attempt a freeze or recall of funds.
7. Can email accounts be traced?
Yes. Through forensic analysis, investigators can trace IP logs, devices, and activity patterns.
8. Should I inform my clients or suppliers?
Yes. Transparency prevents further fraud and protects your reputation.
9. How long do investigations take?
It depends on complexity. Some cases take days, others months.
10. What does a cybercrime investigation cost?
Costs vary depending on scope. Consultation helps define a structured and affordable approach.
Final Word
Business Email Compromise is not just a cyber issue — it is a financial and legal crisis.
The difference between recovery and loss often comes down to how you respond in the first 24 hours.
If you are affected, act fast — and act correctly.
PI INVESTIGATOR is here to guide you.
